Top Guidelines Of Linux Foundation Discount Linux Foundation Cyber Security
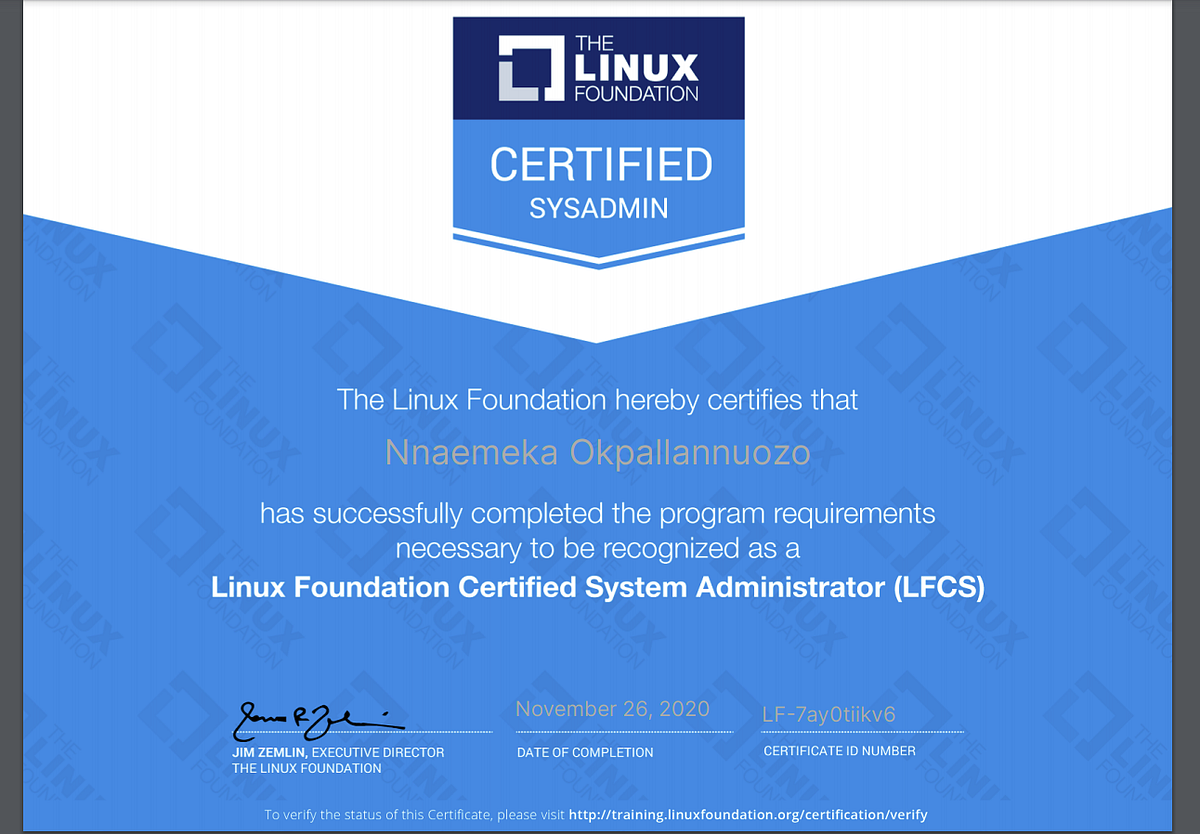
This Linux training is thought about admin-level Linux Structure training, which means it was designed for systems administrators (Linux + Certification). Linux foundation cyber security. This LFCS course is valuable for brand-new IT professionals with at least a year of experience with Linux and experienced systems administrators wanting to verify their Linux Structure abilities. New or ambitious systems administrators. Linux foundation cyber security.
New sysadmins are going to need Linux, and this certification should offer your profession a great increase and you a leg up on the competitors. Experienced systems administrators.
Linux Foundation Cyber Security Getting My Linux Foundation To Work
Hands-on Labs are directed, interactive experiences that help you find out and practice real-world scenarios in genuine cloud environments. Linux foundation cyber security. Hands-on Labs are effortlessly integrated in courses, so you can find out by doing.
They must guarantee the computer systems are following the security practices and developed guidelines., details innovation, information science, telecom or any other associated field.
All about Linux Foundation Certified Linux Foundation Cyber Security
Linux foundation cyber security. If you still can’t discover what you’re looking for, attempt utilizing the search feature by clicking the magnifying glass icon above. CSS And Java, Script Shows Language And Python Programs Language Total Course 6 Realistic Practice Tests Updated Practice Test Covers The Whole Test Curriculum 6 Newest Practice Test With NEW 2021 CEHv11 Topics Practice and Pass Exam Be a Certified Ethical Hacker Start Live, Streaming and Recording to Jerk, You, Tube, Mixer & more utilizing Open Broadcaster Software application (OBS Studio) Sign up with 150,000+ students – Discover cyber security, penetration testing (pentesting) and ethical hacking, How To Install WordPress On Your Domain And How To Configure Fundamental Pages.
Linux Foundation Cyber Security The Linux Foundation Discount PDFs
Red Hat, RHCSA, RHCA, RHEL, Red Hat Certified Engineer and RHCE are hallmarks or signed up trademarks of Red Hat Inc. ITGilde and its members are not connected with the trademark owner.
You can’t carry out that action at this time.
How Linux Foundation Certified Systems Administrator can Save You Time, Stress, and Money.
How to Prepare for the LFCS Exam? Preparing for the LFCS Linux Foundation Certified System Administrator Certificate exam? Do not know where to start? This post is the LFCS Certificate Study Guide (with links to each test goal). Linux foundation cyber security. I have curated a list of posts from Microsoft documentation for each goal of the LFCS test.
I receive a commission when you acquire through them. Essential Commands 25% Log into regional & remote graphical and text mode consoles Browse for files Evaluate and compare the fundamental file system features and choices Compare and control file material Usage input-output redirection (e. g (Linux Foundation Certified). >, >>,, 2 >) Evaluate a text utilizing standard regular expressions Archive, backup, compress, unload, and uncompress files Create, delete, copy, and move files and directories Produce and handle difficult and soft links List, set, and alter basic file consents Check out, and usage system documentation Manage access to the root account Operation of Running Systems 20% Boot, reboot, and closed down a system securely Boot or change system into various operating modes Set up, configure and troubleshoot bootloaders Detect and handle procedures Find and examine system log files Schedule tasks to perform at a set date and time Verify conclusion of arranged tasks Update software application to provide necessary functionality and security Verify the stability and schedule of resources Confirm the stability and schedule of crucial procedures Change kernel runtime criteria, relentless and non-persistent Usage scripting to automate system upkeep tasks Manage the startup procedure and services (In Services Setup) List and recognize SELinux/App, Armor file and procedure contexts Manage Software Determine the part of a Linux circulation that a file belongs to Amazon link (affiliate) User and Group Management 10% Develop, delete, and modify regional user accounts Create, erase, and modify local groups and group subscriptions Manage system-wide environment profiles Manage design template user environment Configure user resource limits Manage user opportunities Configure PAM Networking 12% Configure networking and hostname resolution statically or dynamically Configure network services to begin automatically at boot Implement packet filtering Start, stop and examine the status of network services Statically path IP traffic Integrate time utilizing other network peers Service Setup 20% Set up a caching DNS server Maintain a DNS zone Configure email aliases Configure SSH servers and clients Restrict access to the HTTP proxy server Configure an IMAP and IMAPS service Inquiry and modify the behavior of system services at various running modes Configure an HTTP server Configure HTTP server log files Configure a database server Restrict access to a web page Manage and set up containers Manage and set up Virtual Makers Storage Management 13% List, create, delete, and customize physical storage partitions Handle and set up LVM storage Produce and set up encrypted storage Configure systems to install file systems at or during boot Configure and manage swap area Develop and manage RAID gadgets Configure systems to mount file systems as needed Produce, handle and identify innovative file system permissions Set up user and group disk quotas for filesystems Develop and set up file systems. Linux foundation cyber security. This brings us to the end of the LFCS Linux Structure Qualified System Administrator research study guide. Linux foundation cyber security.
